Open DMR Terminal Protocol/Push Service Revision as of 13:36, 8 February 2019 by R3ABM (Talk | contribs) (→Terminal requests BM to register push-channel)
Contents
DRAFT
Conditions
- Since publishing "FCM HTTP v1" Google improved security system of their FCM services. Now it requires to use short-time access tokens of OAuth 2.0 service, which uses private key based authentication and specific Google software libraries.
- Each terminal vendor has it's own application with it's unique Application ID registered and Google Firebase. Terminal may have several applications with different IDs. It should not be a good idea to hardcode Application IDs inside BM's code as well as vendor's private key to pass Google Authentication.
- Due to real-time nature of the service all messages should be sent by BM directly. This should solve issues of inaccessability of service and power of vendor's site.
Assumptions
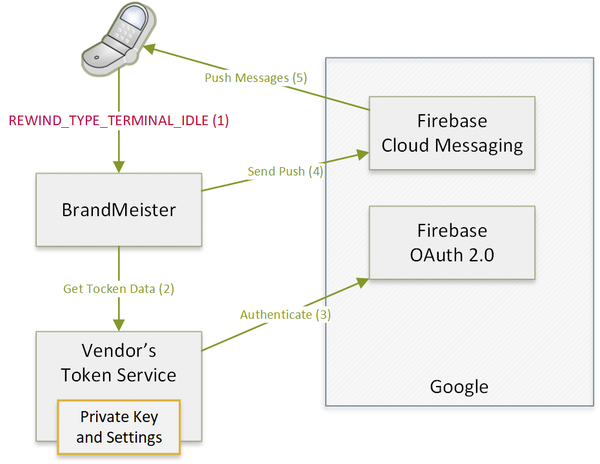
- When terminal goes to the idle mode it may pass IDLE message to BM contains info about Vendor's service which will provide information to pass messages to FCM such as application identifiers, access token and expiration time.
- On this way terminal vendor delegates message sending feature to BM without disclosing information of its private key.
- BM / Registry will store these data and assosiate it with particular terminal / connection context and use it to wake application up.
Scenario
- After logging-in to BM a terminal application sends message REWIND_TYPE_TERMINAL_ATTACH with data of TokenService URL and device token
- When terminal application needs to go background or exit it sends to BM a messasge REWIND_TYPE_TERMINAL_IDLE to switch connection to stand-by mode
- When BM needs to send something to a terminal application it checks local database for suitable access token and application ID *A1
- BM sends push message to terminal application using suitable access token and project ID
- Terminal application receives push message from FCM
- Terminal application goes online and reconnects to BM using message REWIND_TYPE_KEEP_ALIVE
A1. Token information not found:
- BM queries <URL of token service> for application and token info
- Token Service does authentication at Google OAuth 2.0 service using its private key
- Token Service passes application-id, access-token and expiration-time to BM
- BM stores access token and application ID in its database
Security
- Terminal may add a verification string to URL of token service to check that request of token initiated by vendor's application, it could be something like CRC32 hash of BM's IP salted with secret known only to terminal and token service.
- BM will call token service only in following cases:
- token not found
- token expired
- FCM returned code 401
Examples
Terminal requests BM to register push-channel
Please check main article for actual binary format!
[REWIND_TYPE_TERMINAL_ATTACH] http://my-dmr-vendor.com/token/?code=123456 jhsdfjasdfsdfeTERTcxvvxerSR
Where
- http://my-dmr-vendor.com/token/?code=123456 is address of TokenService to provide OAuth 2.0 token for FCM authentication,
- jhsdfjasdfsdfeTERTcxvvxerSR is a device token to deliver messages to
BM requests Token Service
GET http://my-dmr-vendor.com/token/?code=123456
Token Service responds to BM
<syntaxhighlight lang="JavaScript"> {
type: 'FCM HTTP v1', project: 'mydmrapp-jaso42', token: 'isdmlifdlWERWdsfWsdfsfsdfWER', expires: 3600
} </syntaxhighlight>
Where:
- mydmrapp-jaso42 - Google's project ID for application
- isdmlifdlWERWdsfWsdfsfsdfWER - FCM OAuth 2.0 token
BM sends Push to an application
<syntaxhighlight lang="JavaScript"> {
"message":
{
"token" : "jhsdfjasdfsdfeTERTcxvvxerSR",
"data" :
{
"type" : "data"
"body" : "<base64-encoded REWIND datagram>"
},
"android":
{
"priority": "high",
"ttl": "0"
}
}
} </syntaxhighlight>
 BrandMeister
BrandMeister